 CAN data to Android Device for Automotive
CAN data to Android Device for Automotive Communication Devices
Communication Devices r
r

Custom Automotive App Solutions


Custom Controls Power System Development
 Software DevelopmentElegant and Flexible
Software DevelopmentElegant and Flexible
 Artificial Intelligence in Embedded Systems
Artificial Intelligence in Embedded Systems
Gwentech develops software and electronic hardware products for automotive and industrial markets.
Integrity ● Trust ● Quality ● On-Time ● Flexible
SERVICES
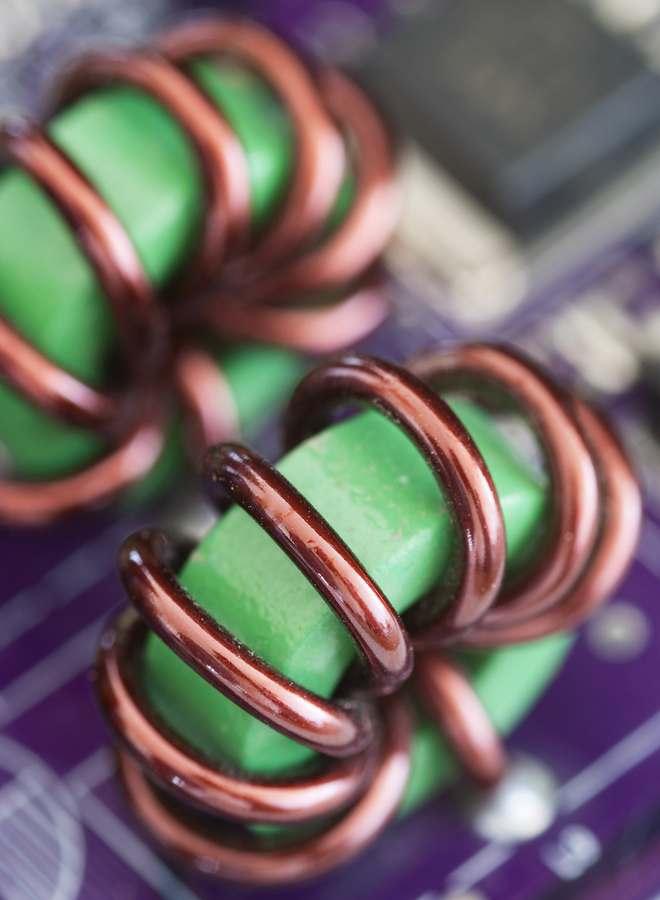
Electronic Hardware
DSPs · Power Circuits · Real-Time Control · Custom Interfaces · Analog Circuits · Wireless
Read More>>Software Design
Embedded Firmware · Web Applications · PC Applications · Mobile Apps
Read More>>PRODUCTS
Development Tools for Engineers
Read More>>OUR SKILLS
Here's how we rate our skills. If your project involves anything outside of our skillset, just ask anyway. Chances are, we know someone who can fill in the gaps.
Electronic Design
Using a chainsaw
Coding
Playing Golf
Communication
TESTIMONIALS
'Thanks to Gwentech for their product and assistance. They provided excellent support for both hardware and software'.
'Gwentech delivered a custom variation of their product in record time for a concept design. We look forward to future business with them!'
'Gwentech was very responsive in helping us prototype our concept with their GT1026 product. Thanks for your part in making our project a success!'
CONTACT










